Ever fantasized about playing with docker misconfigurations, privilege escalation, etc. within a container?
Download this VM, pull out your pentest hats and get started :)
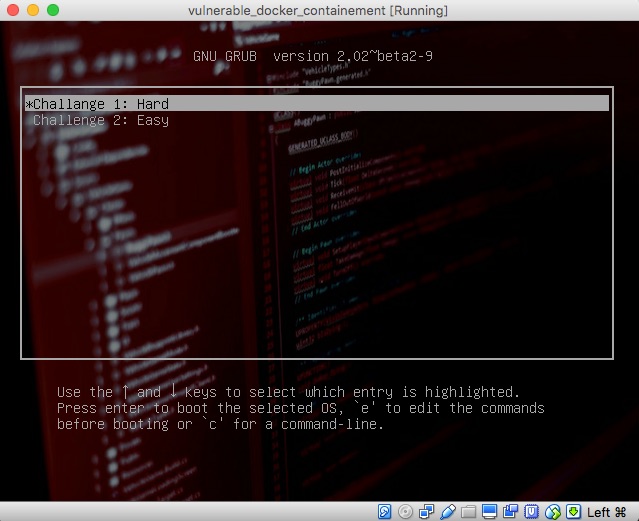
We have 2 Modes:
- HARD: This would require you to combine your docker skills as well as your pen-testing skills to achieve host compromise.
- EASY: Relatively easier path, knowing docker would be enough to compromise the machine and gain root on the host machines.
We have planted 3 flag files across the various machines / systems that are available to you. Your mission if you choose to accept would be as following:
1. Identify all the flags (2 in total: flag_1 and flag_3) (flag_2 was inadvertently left out)
2. Gain id=0 shell access on the host machine.