Wordpress 2.1.2 xmlrpc Multiple Vulnerabilities:
Affected Versions: These issues were reported in version 2.1.2,(current stable version) and its very likely that previous versions may also be vulnerable.
1. Privilidge Escalation:
Under normal circumstances (through web interface) a user in contributor role only has access to following functions:
a. read
b. edit_posts
functionality 'publish_posts' is restricted to users in the author, editor or administrator roles. However, this is not implemented in xmlrpc.php and this allows a user in the contributor roles to publish a previously saved post to the website.
No exploit code is required.
2. SQL Injection:
This is only exploitable by authenticated users.
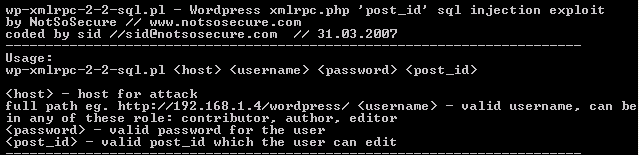
The post_id parameter is not properly sanitized before passing its value to the backend database which results in a Sql injection. Exploiting this is pretty trivial. As, it is an integer based injection, it works irrespective of the setting "magic quote". I wrote a Simple Proof Of Concept for this.
Download Exploit
-----------------------------------------------------
-----------------------------------------------------
Successful Exploitation of this will give you usernames and md5 hash of password of all users including admin user. Before you run mdcrack on this hash, read my previous post on wordpress cookies as this will save your time.
Once you have the admin user hash needless to say you can create a php backdoor and that essentialy is game over.
About Poc:
The poc demonstrates how critical SQL injection vulnerabilities can be. In this example,the poc goes beyond obtaining admin hashes. It also returns the username and encrypted password of the mysql user(s). If the database is running as privilidged user, this will also try to fetch the /etc/passwd file, or any other file for that matter. As this injection is in an integer field it works irrespective of the setting magic quote :-)
Workaround:
1. Disable xmlrpc if you dont use it or restrict its access to trusted users only.
Vendor's response:
1. vendor notified on 22nd March 2007.
2. New Version released on 2nd April 2007.
3. Advisory released on 2nd April 2007
-------------------------------
Advert: Testking provides highest quality 000-083 exam dumps, 000-085 video demos and 000-100 practice tests with 100% pass guarantee